No one picks up calls from unknown numbers anymore, almost. I know, because I ask everyone I meet this question – do you pick up calls from unknown numbers?
The answer is universally the same – a sigh of frustration, and a wry smile, followed by “No, I don’t. Just too many spam calls”.
In an era where voice calls face declining answer rates and rising fraud, Call Branding has been pushed as a solid solution to enterprises aiming to restore trust in phone-based customer engagement. But what is it? How does it work? What’s the tech behind it all? Let’s dive into that rabbit hole!
But before we go in – a disclaimer: This isn’t an investigation that gets done in one article – an industry that is expected to grow at 1,720% to become worth 2.3 billion USD by 2030 needs more than one little writeup – so I’m gonna break it up into multiple parts – releasing one every two weeks. Hope that works for you, kind reader – your patience is much appreciated.
In this series of articles, I take a high-level look at the major approaches to Call Branding currently in use across the US and India, along with their capabilities, limitations, and technical underpinnings. Why US and India? Because that’s all I know! Maybe in the future, I will look at other geos as well.
Let’s begin with some tech being used by the US telcos – STIR/SHAKEN and Rich Call Data.
The US Telco approach to Call Branding
The first thing that Americans are trying to solve is the problem of number spoofing – As a telco, you receive a message from a peer about a call, originating from number X. You accept this and pass on the call to the receiver Y, and later find out that the number X was fake, because the peer had replaced the original number with X. More commonly, the peer network itself may have received the call from another network, which claimed that X was the caller, but how you know?
The solution – STIR/SHAKEN!
STIR/SHAKEN
STIR/SHAKEN is a combination of two protocols designed to work together.
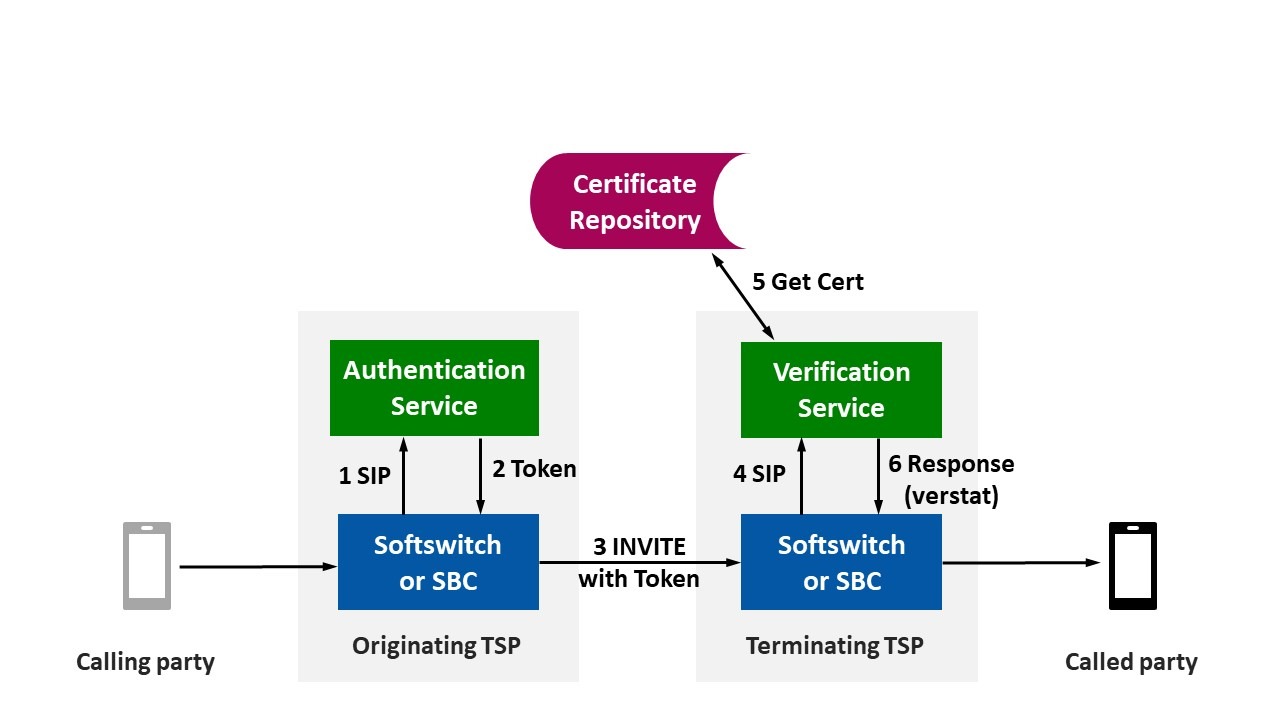
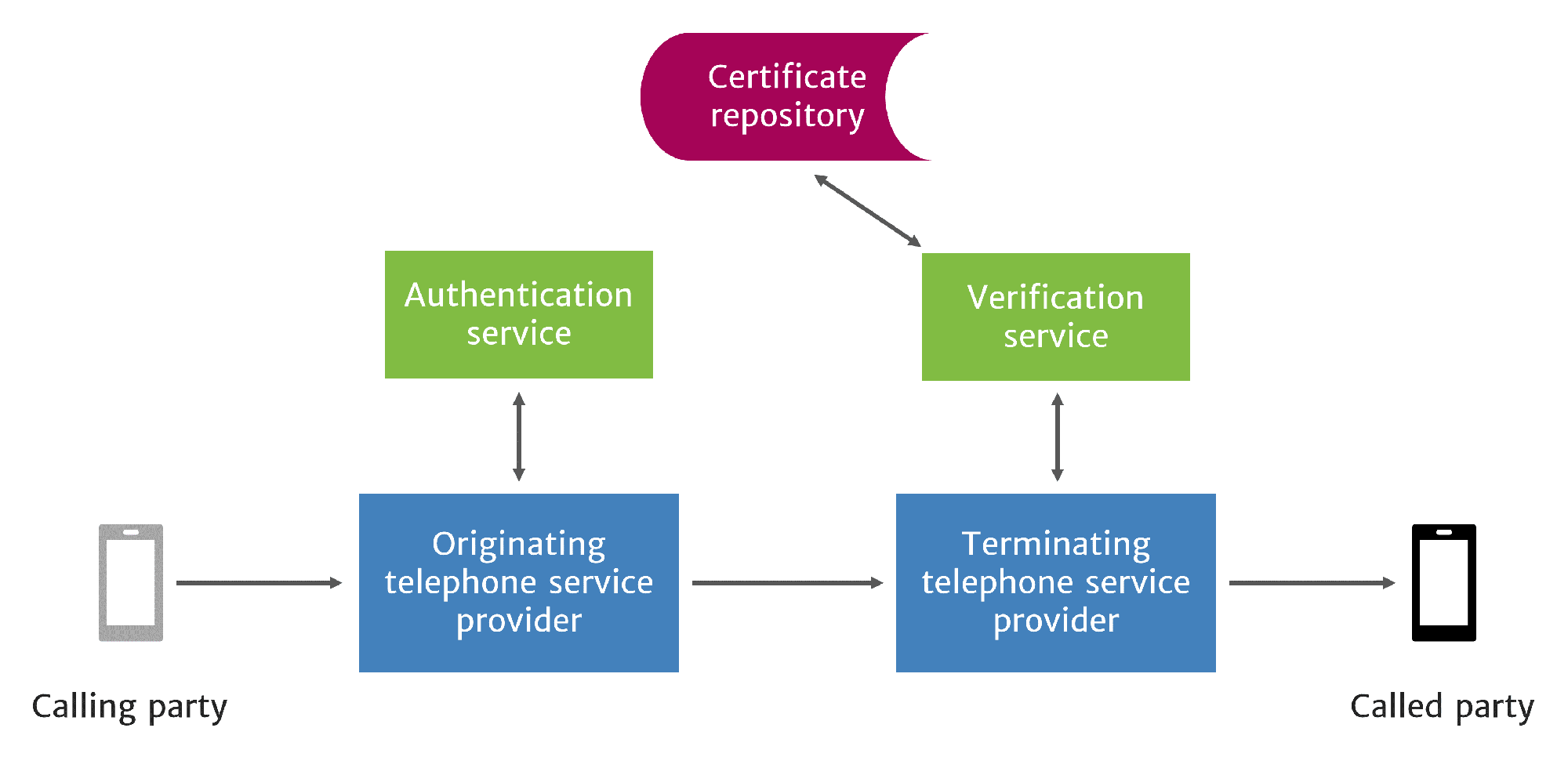
STIR – Secure Telephone Identity Revisited: Pushed by the FCC and developed as an industry standard, STIR is a set of protocols that use a combination of digital certificates and public key cryptography to authenticate the calling party’s identity and right to use a phone number. As part of this, calls are accompanied by a cryptographic signature, which can be used to verify that the caller ID has not been tampered with.
SHAKEN – Signature-based Handling of Asserted Information Using toKENs: A set of guidelines for implementing the STIR protocol across interconnected phone networks, ensuring that calls are signed by originating carriers and verified by terminating carriers before reaching consumers
Obviously, the next protocol these guys develop will be called Dry Martini
Anyways, the summary of this whole James Bond story is that when you receive a call from a number, your phone will essentially be able to confirm that the calling number is not spoofed. This, in turn, comes with 3 levels of guarantees, formally called ‘attestations’:
- Level A (Full Attestation): In this, the telephony network can state with full confidence that:
- The caller is fully authenticated and authorized
- The caller number is verified to belong to the caller
- The call originated from an authenticated subscriber on the provider’s network.
- B (Partial Attestation): At this level, some uncertainty creeps in.
- Caller is probably correct but not fully authenticated
- The call originated from the provider’s network, but they could not fully verify the calling party’s right to use the number (e.g., reseller calls).
- C (Gateway Attestation): At this level, no one knows anything.
- The call originated outside the service provider’s network. For example, the call was received from an unverified or foreign source (one that does not support STIR/SHAKEN), so the provider cannot confirm legitimacy.
Rich Call Data
So, STIR/SHAKEN ensures that the calls you receive are NOT from spoofed numbers, but they still don’t tell you WHO is calling. Call Branding – the subject of this piece, is all about making sure that calls come in with context. Rich Call Data (RCD) is the technology standard that lets enterprises attach rich content—such as the business name, logo, and call reason—to outbound calls.
In later articles, I will do a deep dive into the STIR/SHAKEN/RCD tech, but for now – here are the key takeaways:
- STIR/SHAKEN gives you the confidence that the caller is not spoofing the number.
- But by itself, it is NOT a branding tech! For that, you need RCD!
How this works in real life
The call flow model is as follows:
- Enterprises work with telcos (or more commonly, partners of telcos) to verify and certify businesses during the onboarding process to ensure that only legitimate callers are allowed to send branded data.
- When the enterprise initiates an outbound call, the telco (or its partner) cryptographically signs the call, using the STIR/SHAKEN framework. This cryptographic signature validates that the call is legitimately coming from the phone number and business it claims to represent.
- The originating carrier and the terminating carrier both participate in creating and verifying this signed caller identity. If the signatures don’t match – it’s a signal of tampering. If the signatures are not present, the call is marked as Level C – the telco is essentially telling the phone that it does not guarantee anything about the call – and the phone can then show this info to the recipient.
- If the calling enterprise has signed up for RCD, it can also attach its logo, brand name, and call reason and if the call is a high-trust call (Level A), the phone will display this to the recipient.
Naturally, enterprises that sign up for this pay extra for each call, after all the onboarding verification, the cryptographic infrastructure, the RCD messaging – all these take work and effort. But the benefit is – much higher call pickup rate, all because customers know who’s calling!
In the next article, I will explore the Call Branding solution used in Airtel India’s Business Name Display system.
